Symantec has released the 2018 Internet Security Threat Report (ISTR) and it is clear that the threat landscape is more diverse than ever. Cyber criminals are developing new ways to attack business networks, databases, PCs, WiFi, mobile phones...all with the aim of extracting information, money or influence, and covering their tracks while doing so.
Coin Mining
The staggering increase in the value of cryptocurrency in 2017 drew the focus of attackers who had previously relied on ransomware attacks for their nefarious income. Coin mining is a tactic of infiltrating computers with a few lines of code, which then allows miners to use the infected PC’s processing power and cloud CPU usage to mine for cryptocurrency, such as Bitcoin.
Whilst coin miners don’t usually demand any financial ransom from the business owners, there are still negative impacts of being a victim. The main issues that businesses face are performance related, such as slower devices, overheating, and even making some devices unusable. Financial ramifications include charges from your Cloud provider for the Cloud CPU usage by the coin miners.
Software Supply Chain Attacks
Because it is getting harder for attackers to detect vulnerabilities at the end point, attacks during the supply chain are becoming more common. The number of these type of attacks has risen by 200% from once a quarter to once a month in 2017.
Software supply chain attacks occur when an attacker infects software before it is downloaded, by infiltrating the software vendor rather than the end target.
An example: An attacker compromises the website of a software vendor, replacing a legitimate software upgrade with their own version that has been infected with malware. When the software is downloaded, the malware enters the victim’s network. Because the software that was downloaded was a copy of the real version, the victim often doesn’t suspect anything is amiss.
Ransomware

There was good news for ransomware victims in 2017, with the average ransomware demand dropping to half that of previous years, to undefined. There was also a drop in prolific ransomware families, although they were diversifying the strains of attacks that were being launched, with a rise of 46% in different ransomware variants.
Mobile Malware

Mobile phones are here to stay, and that means that criminals are focusing their efforts on mobile malware. Year on year there was a 54% increase in the number of mobile malware variants released in 2017. The usage of outdated operating systems exacerbates the effectiveness of mobile malware. Only 20% of Android™ devices run the latest major version of the OS, and only 2.3% or on the latest minor release. This means that attackers can take advantage of security vulnerabilities that later OS versions have resolved.
Grayware is on the rise too. Grayware is a type of adware that has the sole purpose of making advertising money off your data, and in some instances criminal uses for your information. Grayware is commonly downloaded along with an App which you might have intentionally downloaded, you just didn’t know that it would also be tracking your data, location and mobile phone usage! Whilst the apps that use grayware are not overtly malicious, 63% have been found to leak the mobile phone number and 37% leaked the device location, which raises privacy concerns for victims.
Prevention is better than crisis
So how can you keep safe against these threats?
In some instances, unfortunately there is no way to avoid becoming a victim. Zero Day Attacks that exploit previously unknown vulnerabilities are extremely hard to prevent. Supply chain attacks are another hard-to-detect threat, especially as the software vendor doesn’t normally know something is wrong before the malicious files are downloaded from their own website.
But there are some preventative and quick-to-resolve measures you can take to protect your computers and networks.
-
Install security patches to stop known attacks
-
Run anti-malware scans and anti-virus technology on your end point PCs, networks and mobile phones
-
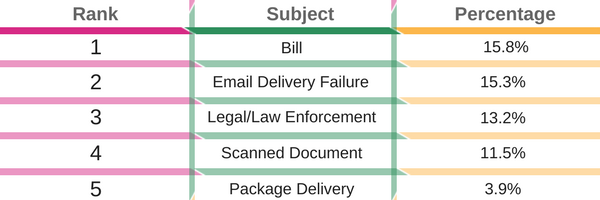
Educate staff so that they can recognise common threats such as malicious email attachments and filenames
-
Top malicious email themes. This table shows the most common themes used in email malware subject lines.
-
We offer a range of IT Security solutions. Enquire using the button below or give us a call!
Date published: 10/04/2018